Proxy for Android
Smartphones in this world are quite a lot of information. Until quite recently, mankind could not imagine such a quantity of functionality in a small and fragile box. Incredible metamorphoses took place at the end of the last century, and now it is only the first half of the 21st.

We can keep in touch with loved ones, have work conversations, share documentation and other files, video and audio materials, and much more. A palette of various applications, entertaining and creative content, photo and video shooting — all this contains such a small item.
Of course, having such functionality, an object cannot be simple. No wonder they say that a modern smartphone is much smarter than a person. There are reasons for this, and if you drop a little deeper, they become very clear.
The active use of mobile phones fell during a very post-war period, one might say in the late 80s or early nineties of the last century. Back then, the smartphone was a little like a modern one, and some lived up to their nicknames of “nutcracker”, because even falling from the 5th floor they didn’t break into smithereens, but only occasionally glitched or spoiled their plastic cases.

Time passed, technology developed and the consumer became more and more demanding and spoiled. One day, the phones completely “disappeared buttons” and only the touch screen we are used to now remained, now almost every person has such a phone, which could not have been imagined in, for example, 2010 because many considered such a luxury.
Now the phone combines many different functions and its contents can become your portrait. Large corporations arrange contextual advertising depending on the applications used and the files filled in the phone. However, the subject is very vulnerable to outside influence for attackers. Data security is an urgent problem that not every operating system can handle. This time we will talk about the Android platform, which is loved by many people around the globe and for good reason because it cannot be said that it is inferior to its competitors.

Initially, Android was a unique autocratic company, but under market pressure and certain financial difficulties, it was bought by Google. Fortunately, this did not negatively affect the product, but only improved an already successful product.
The operating system has a huge pool of smartphone manufacturing companies, with which contracts have been signed for many models in advance.
The popularity justifies itself and Google is actively supporting it by releasing updates and improving its product. Now it is difficult to “get close” to your phone, even for an experienced attacker, because the platform has a lot of layers of protection, through which you just can’t break through. Of course, this does not mean that you can ignore the protection of your data. There are no perfect security systems and everyone can be hacked, it’s just a matter of resources and time. However, we can influence this situation from our side.
As an option: use proxy servers. There are only 2 basic types of proxies:
Free proxies: from the pleasant — they do not require investments to activate their operation. This is where we will end, because if the question is about the safety of the anonymity and data of the client, then this is a very unreliable partner who will aggravate the situation rather than improve it.

Paid proxies: the exact opposite of free ones. Of the minuses, this is the reverse side of the first — they are paid. At the same time, the price tag will not necessarily be sky-high, a proxy is a sought-after product on the market, and prices are always competitive between different companies, which means that everyone can afford them. What can we get when using private proxy servers?
Increased anonymity
Improved network speed and quality
Protection against the influence of intruders
Paid proxies have the support that you can contact with questions.
You can bypass many types of blocking
Keeping track of your actions becomes an almost impossible task.
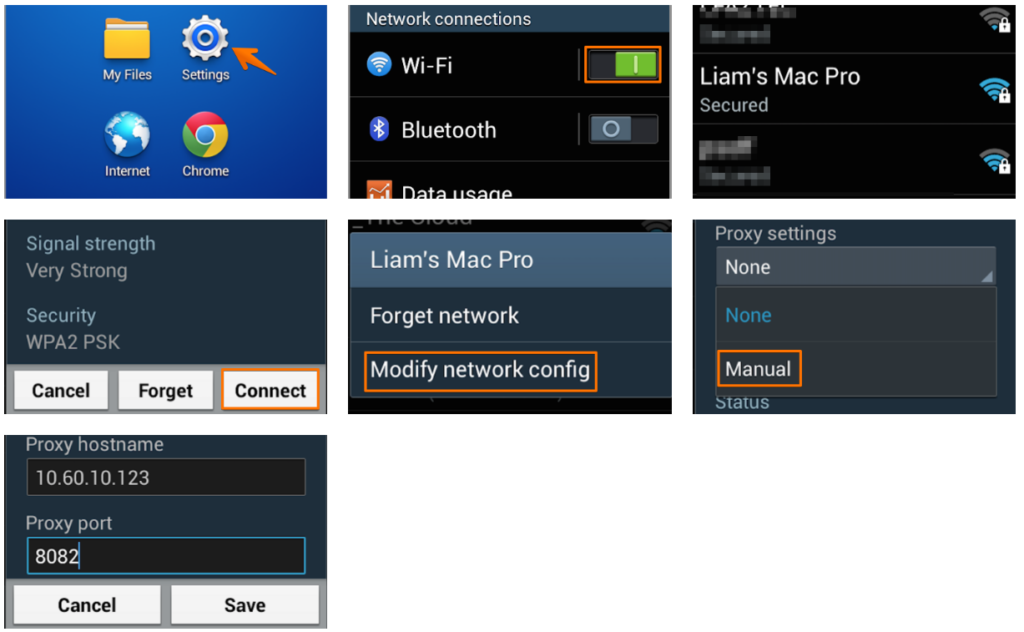
So, to configure a proxy for a Wi-Fi connection, go to:
Settings;
WiFi;
Long press on the desired Wi-Fi network;
In the menu that opens, select: Manage settings;
Show advanced options;
Check the box: Show advanced options;
Proxy > Manual.
After that, enter the IP and port in the appropriate places.
If you have a proxy with authorization by login and password, then the first time you visit a site, an authorization form will appear in which you will need to enter the login and password from the proxy.